Blog
 Pinned
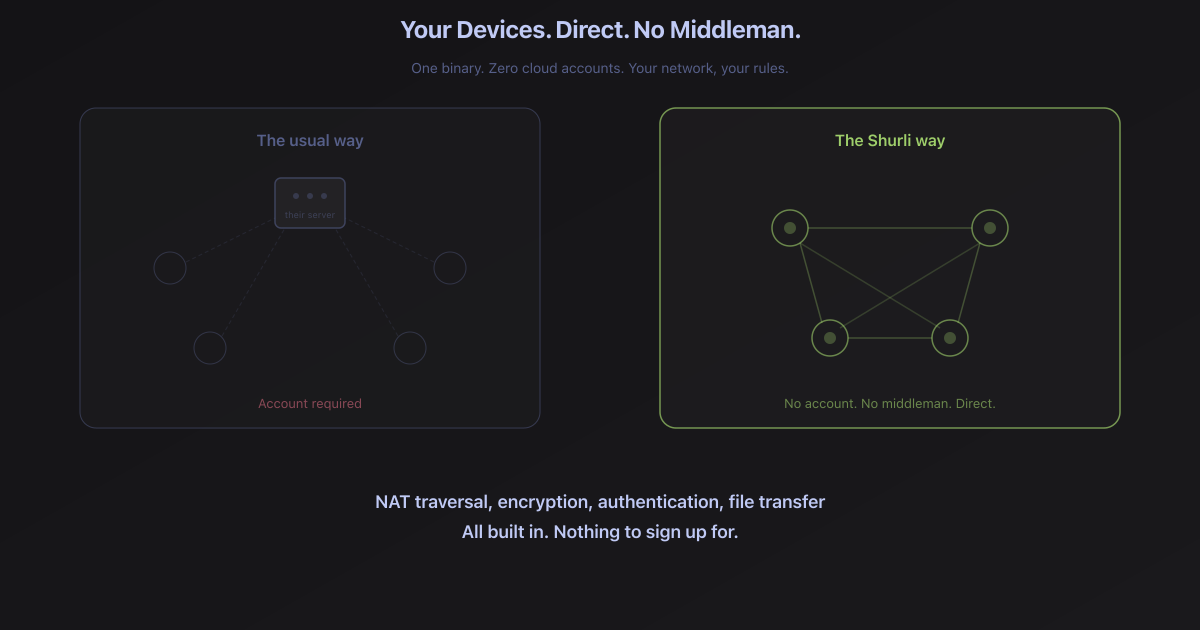
PinnedA factual inventory of what ships in the Shurli binary today: P2P networking, cryptographic authorization, zero-knowledge anonymous auth, private reputation, unified BIP39 identity, full observability. Single binary, zero cloud, zero accounts.
 Pinned
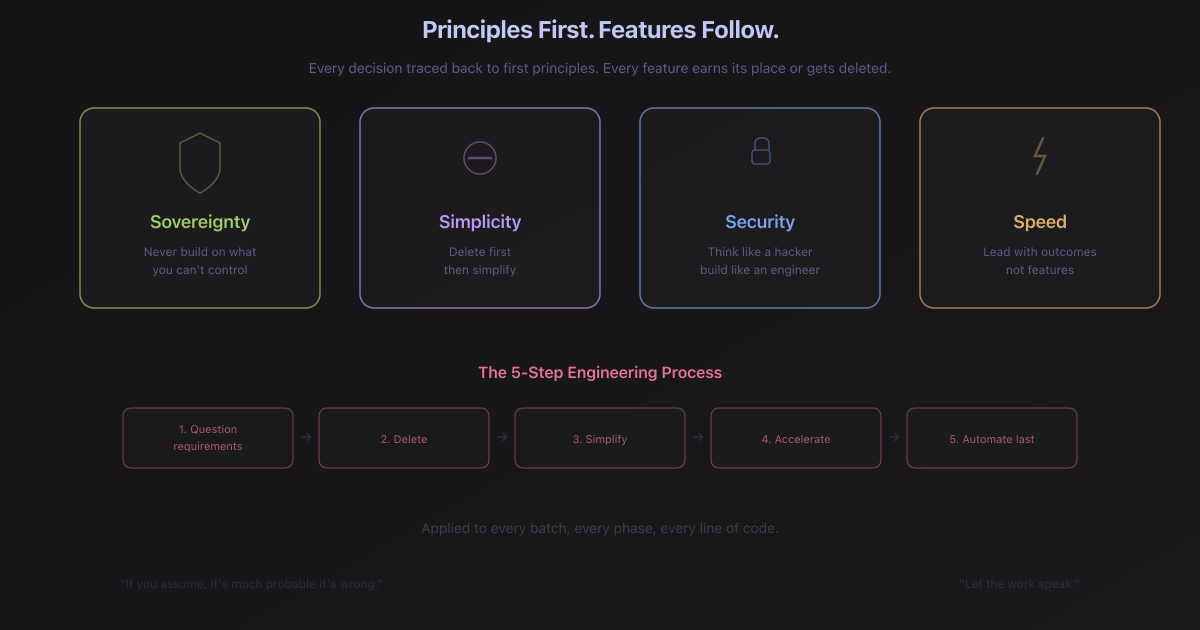
PinnedHow Shurli's engineering principles emerged from real development conversations. The Zero-Human Network vision, AI-native P2P infrastructure, lessons from SuperMesh, and why Shurli was intent-based before the term existed.
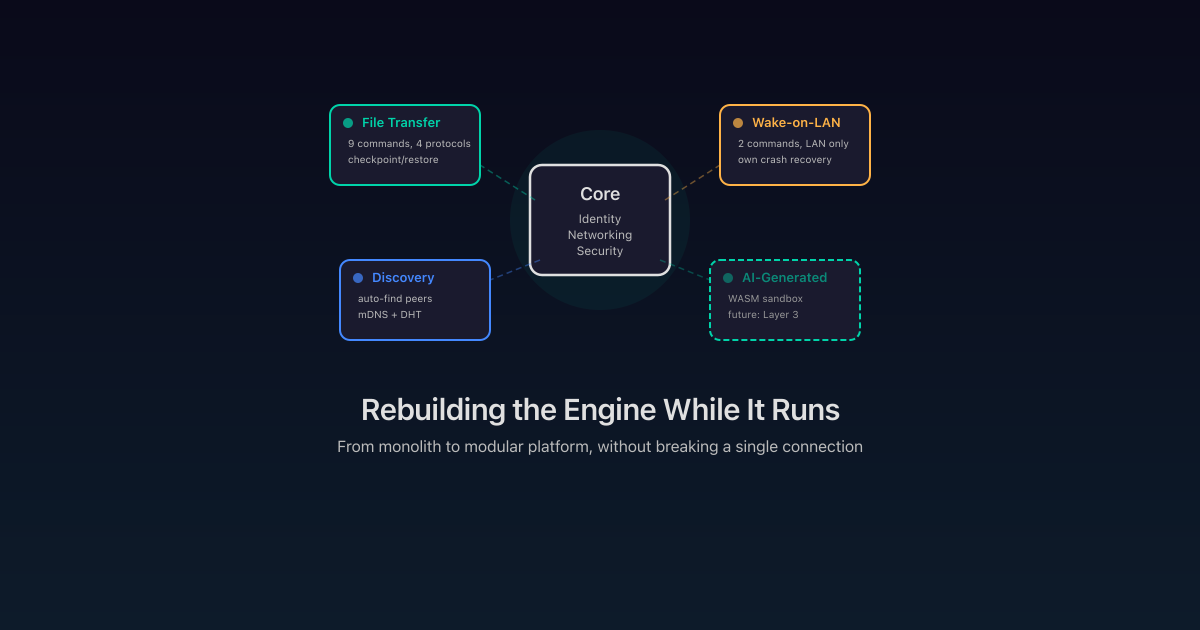
How Shurli went from a single binary to an extensible platform with crash-recovering plugins, transport policies, and a three-layer roadmap toward AI-generated extensions.

We switched WiFi, tethered phones, plugged in cables, and connected VPNs. 16 physical network transitions across 5 network types. Shurli survived all of them without a single restart.
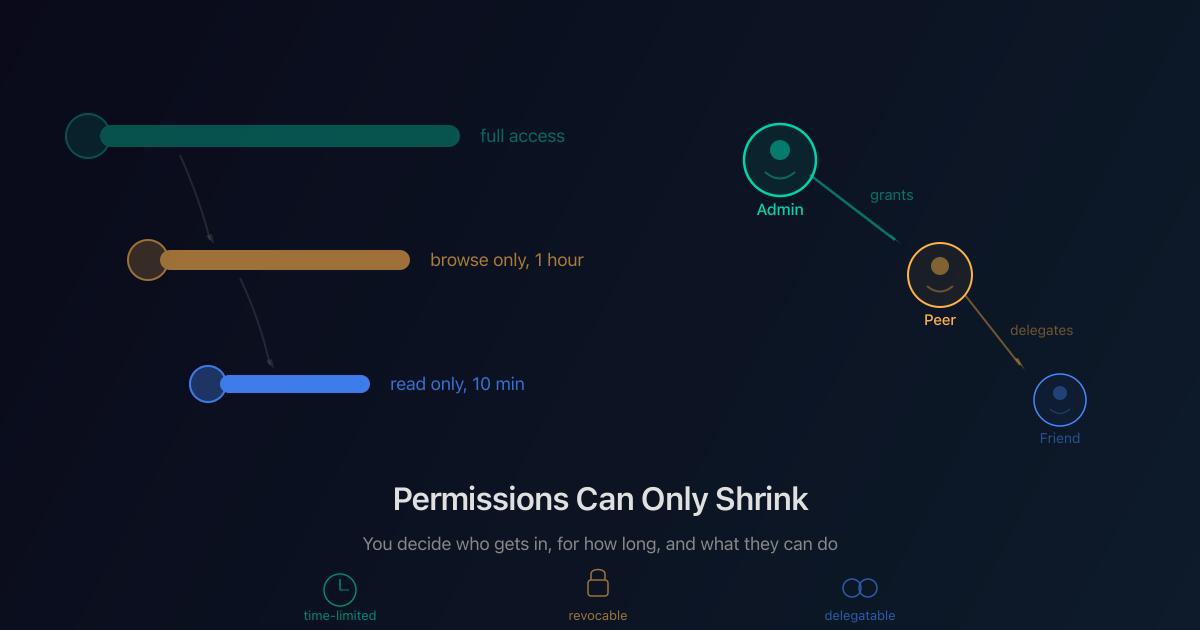
How Shurli controls exactly who can access what, for how long, with cryptographic capability tokens that can be delegated but never widened.
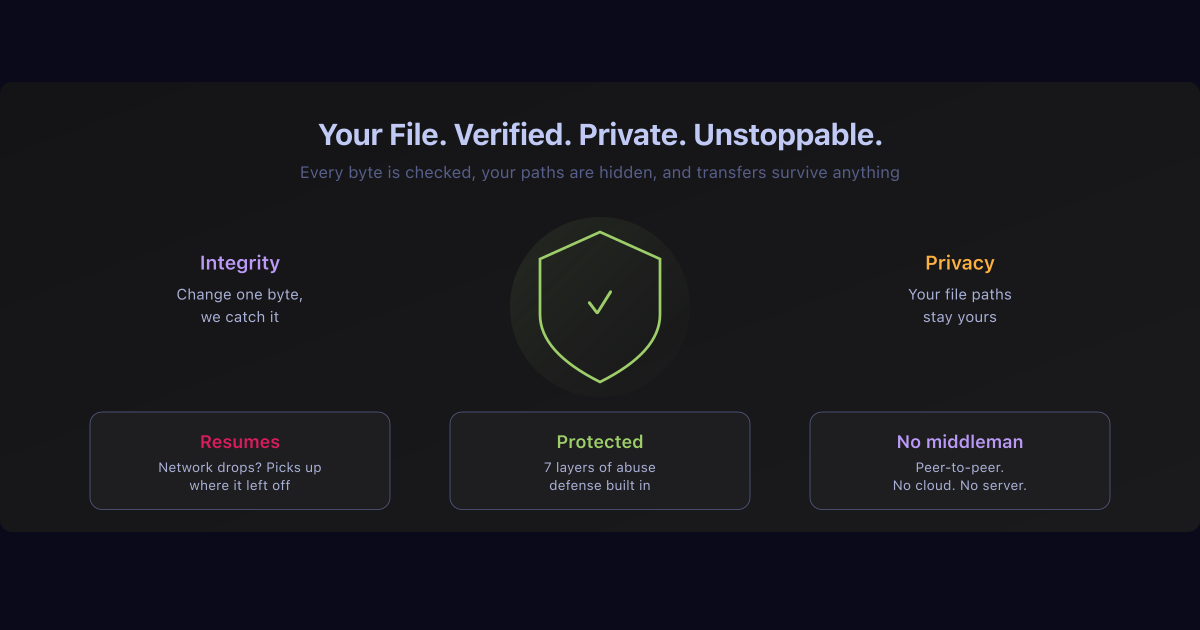
How Shurli's file transfer handles integrity, privacy, DDoS defense, and resume - and what we learned from the gaps in existing tools.
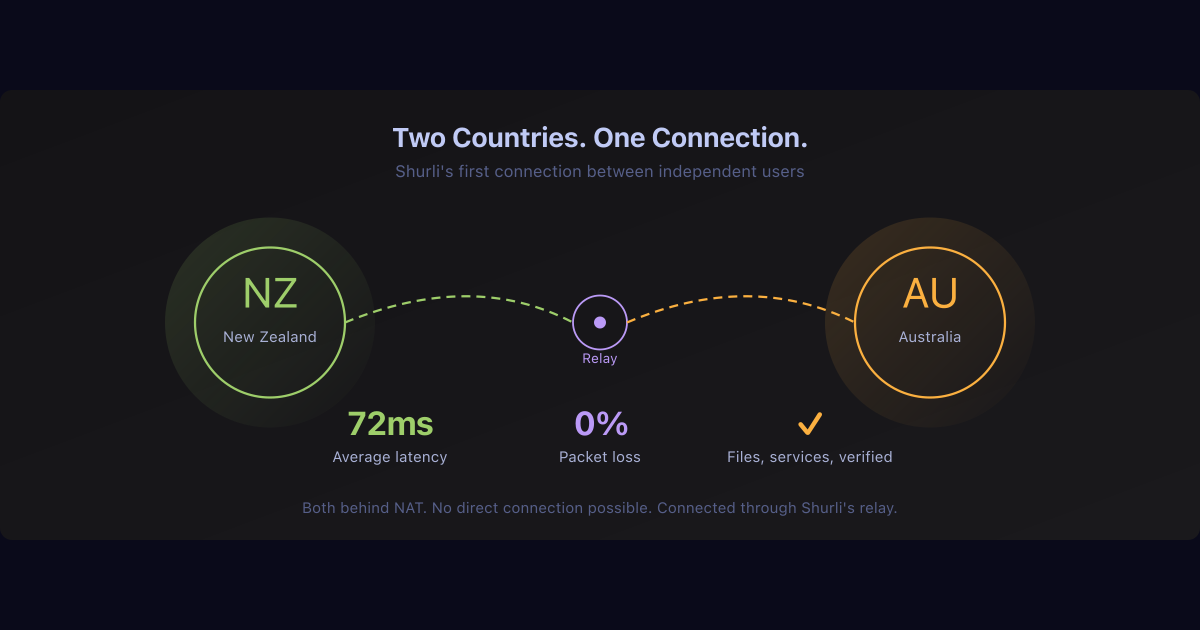
Shurli's first external user connected from Australia to New Zealand through a relay circuit. Here's what worked, what broke, and what we fixed.
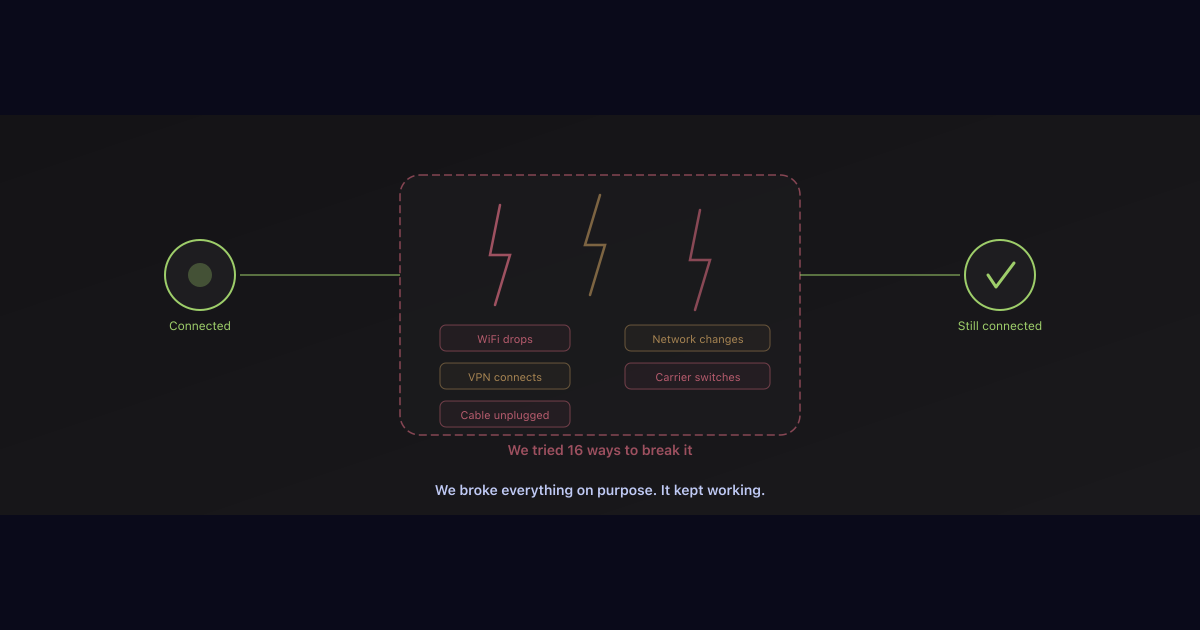
4 days of physical chaos testing across 5 ISPs and 3 VPNs. 11 root causes found and fixed. The daemon now handles every network transition automatically.
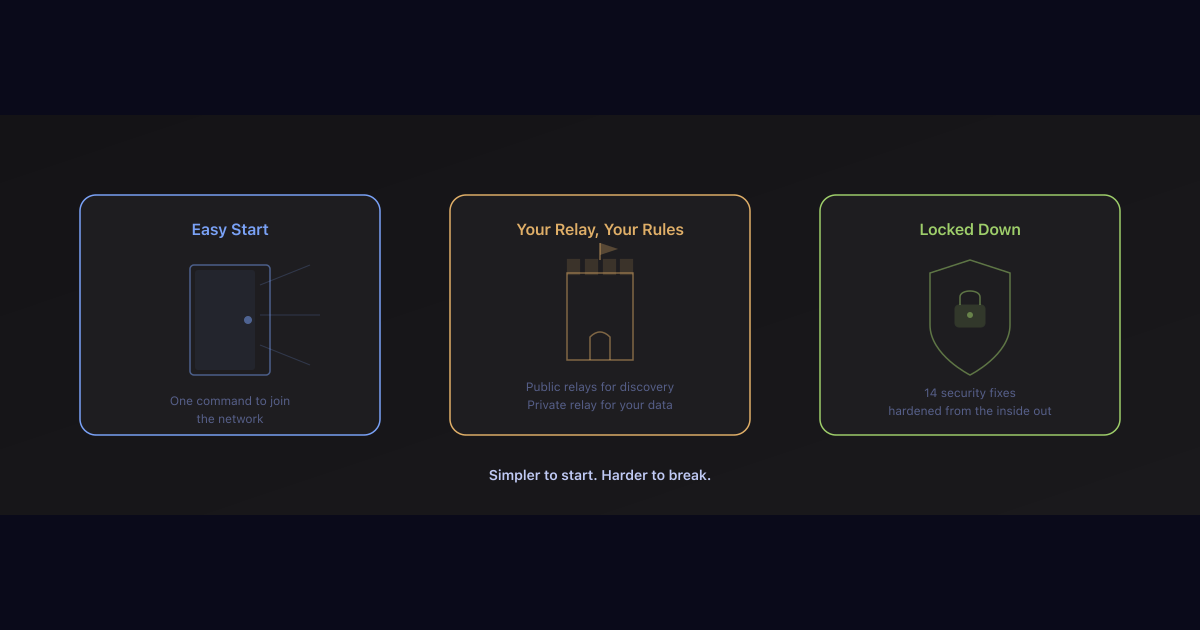
Public seed relays live, async invite flow, relay naming, vault auto-init, 14 security fixes, remote unseal protocol, and DNSSEC. 38 commits, 122 files.

Unified BIP39 seed, encrypted identity, full remote relay admin over P2P, signed operator announcements, session tokens. 24 new files, 56 tests. One backup covers everything.
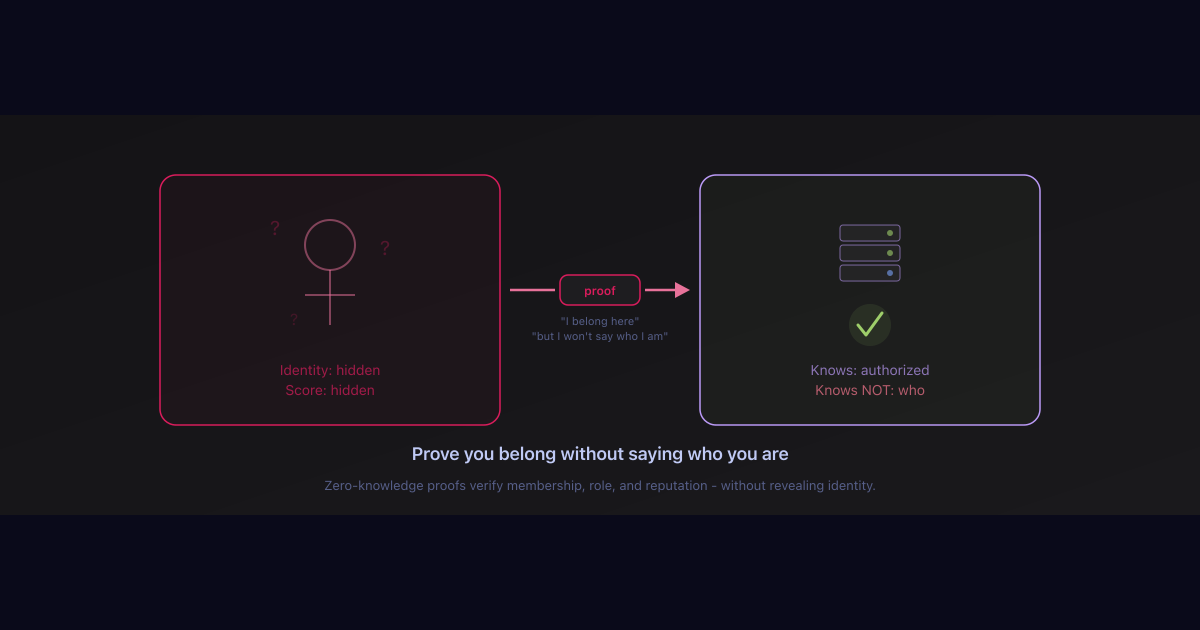
Zero-knowledge membership proofs, private reputation scores, BIP39 key management. 27 new files, 91 tests, 14 Prometheus metrics. L2 blockchain cryptography applied to P2P networking.
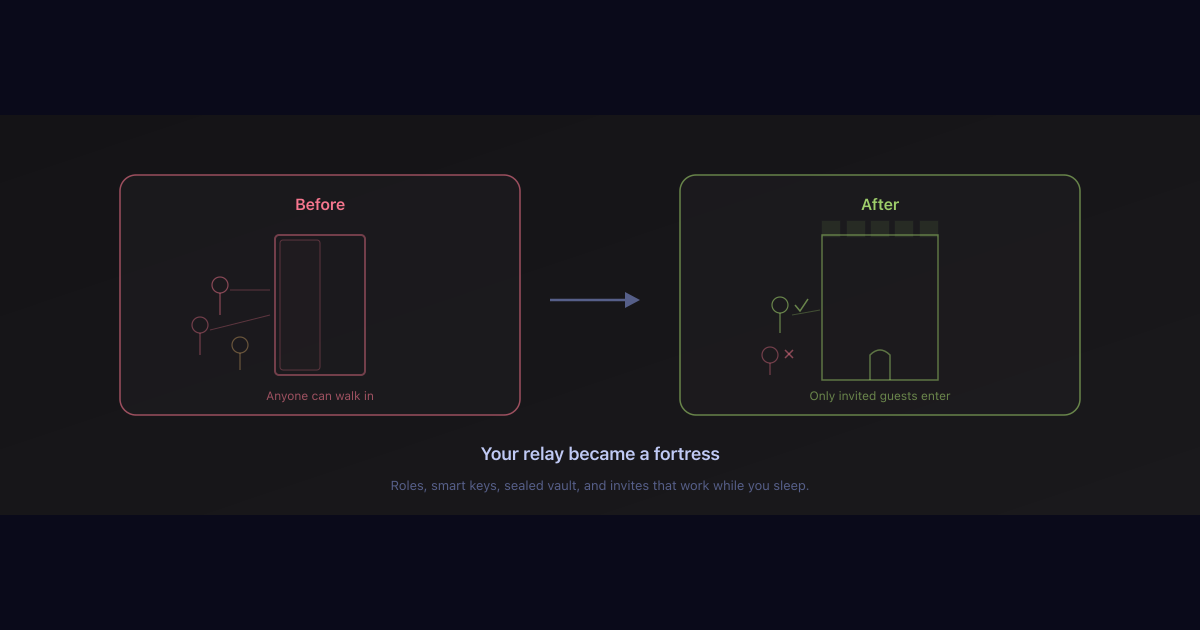
Role-based access, HMAC-chain macaroon tokens, async invite deposits, passphrase-sealed vault, remote unseal over P2P, and two-factor auth. 19 new files, 3,655 lines, zero new dependencies.